Using Dev Proxy to Identify Excessive Microsoft Graph Permissions in Your PowerShell Scripts
Objective
The goal of this article is to show how Microsoft Dev Proxy can be used to audit Microsoft Graph permissions in PowerShell scripts and detect unnecessary scopes. Instead of manually mapping Graph endpoints to permissions, you’ll learn how to automate least-privilege analysis, uncover permission creep, and integrate these checks into your development workflow.
With Microsoft’s Dev Proxy you can use the GraphMinimalPermissionsGuidance plugin to compare the permissions in the JWT that is sent to Microsoft Graph against the permissions needed for each request.
Resolution
Install Dev Proxy
First, we need to install Microsoft Dev Proxy. Microsoft has some great documentation for installing it on Windows, macOS and Linux in an automated fashion or manually. Since I am on macOS I am going to install it using homebrew:
brew tap dotnet/dev-proxy
brew install dev-proxy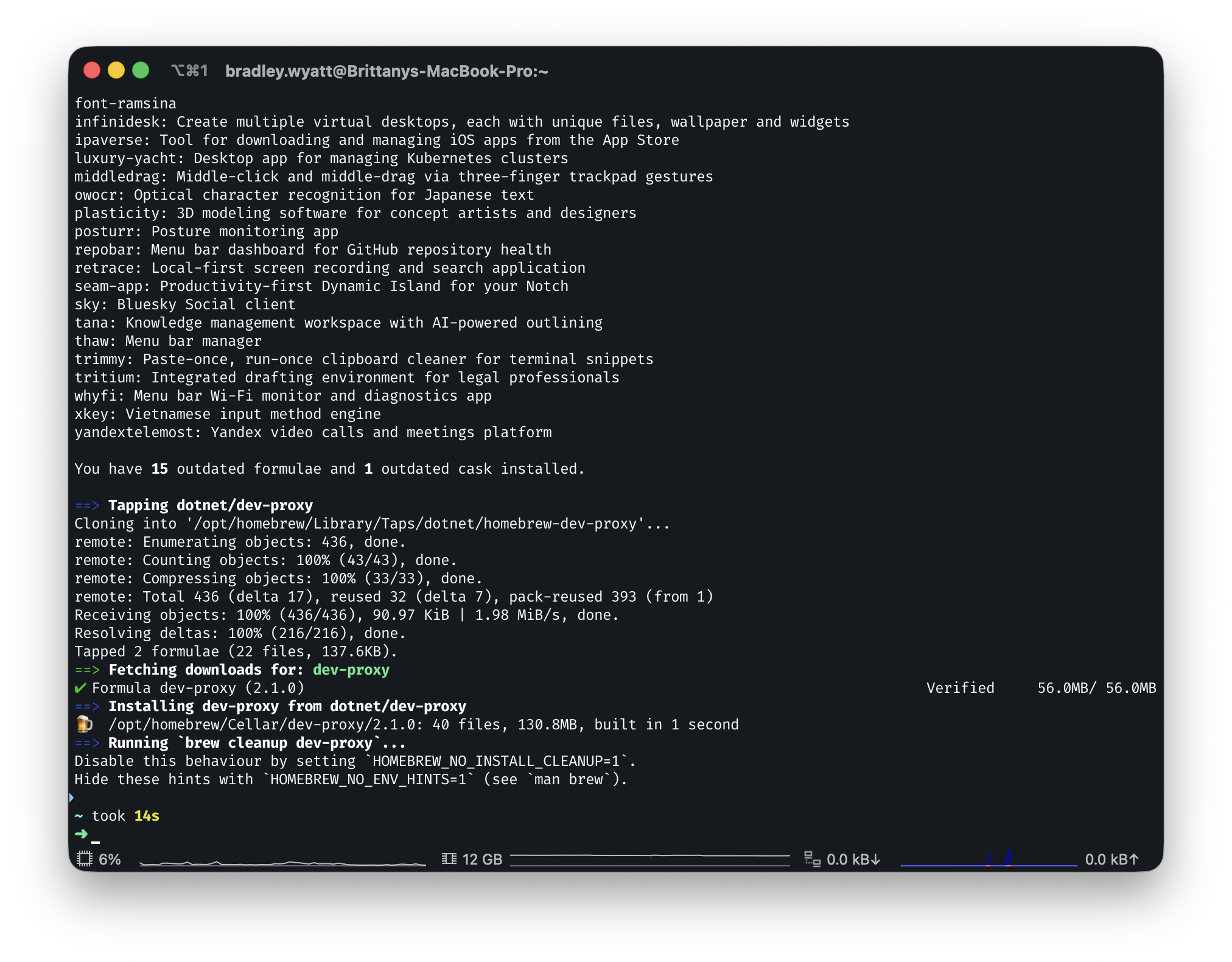
Start Dev Proxy
Once you have it installed, run … Continue...